On the 31st of May 2023, a public warning was issued by MOVEit regarding a critical SQL injection vulnerability found in their systems. This vulnerability allowed malicious actors to gain access to the database. The flaw, known as CVE-2023-34362, was identified on the 2nd of June, but it had already been exploited four days before the alert.
By the end of May, approximately 2,500 instances of MOVEit file transfers were discovered to be exposed online, primarily in the United States. However, major organisations based in the United Kingdom, including the BBC, British Airways, and Boots, have also been affected.
Exploiting these types of vulnerabilities not only enables the extraction of confidential data but also provides initial entry into corporate networks. Ransomware groups have been actively taking advantage of this situation. By the 5th of June, Microsoft attributed these attacks to the Lace Tempest Threat Actor (TA), a group known for its association with Cl0p ransomware and extortion. Moreover, organisations may face indirect repercussions due to data transfers with third parties that use MOVEit file transfer.
“Due to the speed and ease TA505 has exploited this vulnerability, and based on their past campaigns, FBI and CISA expect to see widespread exploitation of unpatched software services in both private and public networks,”
– Joint advisory from the CISA and FBI, 7th of June.
What exactly is an SQL Injection?
SQL injection is a security vulnerability that occurs when an attacker inserts malicious SQL code into a query, allowing them to manipulate or retrieve unauthorised data from a database. It occurs when input from an external source, such as a user, is not properly validated or sanitised before being included in an SQL statement.
Here’s an example to illustrate how SQL injection works:
Let’s consider a simple login form on a website where users enter their username and password to access their accounts. The backend code might look something like this:
SELECT * FROM users WHERE username = ‘<username>’ AND password = ‘<password>’;
The values <username> and <password> would be replaced with the actual input provided by the user. However, if the input is not validated correctly, an attacker can exploit the vulnerability. For instance, the attacker might input the following as the username:
‘ OR ‘1’=’1
When this input is concatenated into the SQL statement, it becomes:
SELECT * FROM users WHERE username = ” OR ‘1’=’1′ AND password = ‘<password>’;
The SQL statement now evaluates ‘1’=’1′, which is always true, and effectively bypasses the password check. As a result, the attacker gains unauthorised access to the system without knowing the correct password.
In a more severe case, an attacker can perform various malicious actions, such as retrieving sensitive data, modifying or deleting data, or executing arbitrary SQL commands. Preventing SQL injection requires the use of parameterised queries or prepared statements, which separate the SQL code from the user input. This way, the input is treated as data and not executable SQL code, significantly reducing the risk of injection attacks.
So, who is behind the MOVEit File Transfer attack?
The Cl0p Ransomware Gang has been active since at least February 2019, engaging in various cybercriminal activities, including operating a ransomware-as-a-service (RaaS) and participating as an affiliate in other RaaS schemes.
The cybercriminal group has been observed acting as an initial access broker (IAB), profiting from compromised enterprise networks. They have also been known to collaborate with other IABs, which highlights the interconnected nature of the modern-day threat landscape. By exploiting vulnerabilities like CVE-2023-34362, an SQL injection flaw in MOVEit file transfer, Cl0p demonstrates its continuous pursuit of zero-day exploits in publicly accessible applications, which are then leveraged to extort victims swiftly and effectively.
It’s important to mention that Cl0p has previously carried out similar large-scale exploitation attacks on other managed file transfer applications, notable examples include SolarWinds Serv-U Managed File Transfer, Accellion FTA, and GoAnywhere MFT, with these attacks dating back to December 2020.
Victims of MOVEit File Transfer attack
Although the exact number of organisations affected by this attack is yet to be confirmed, Cl0p has released an initial set of organisations it claims to have compromised through the MOVEit vulnerability. Cl0p released this list of victims on its dark web leak site, which encompasses well-known names such as energy giant Shell, the University of Georgia in the United States, and investment fund Putnam. Numerous American banks, along with organisations situated in the Netherlands and Switzerland, are included in the list.
Contrasting to the usual approach of ransomware groups, which typically involves reaching out to their victims and demanding ransom payments in exchange for decrypting or deleting stolen files, Cl0p took an unconventional route and did not contact the targeted organisations it had compromised. Instead, a blackmail message was displayed on its dark web leak site, instructing the victims to make contact with the gang before the deadline of June 14th.
Major organisations, including the BBC, Aer Lingus, and British Airways, have previously acknowledged being victims of the attacks because they rely on Zellis, a supplier of HR and payroll software, which confirmed that its MOVEit system had been compromised. UK communications regulator Ofcom revealed that the MOVEit file transfer mass-hack had resulted in the compromise of certain confidential information. In an official statement, Ofcom confirmed that the hackers had accessed data pertaining to the companies it oversees, as well as personal details of 412 Ofcom employees. Transport for London (TfL), the governmental body responsible for operating London’s transport services, and the global consultancy firm Ernst and Young have also claimed to have been impacted by this attack.
Key takeaways
No matter how established you are as an organisation, you need to be confident that your supply chain takes a comprehensive and strategic approach to its security technology, too. To truly stay ahead of widespread cybercriminal groups, we recommend organisations carry out the following:
Need help with any of the above? Our experts are here to help… Get in touch today.
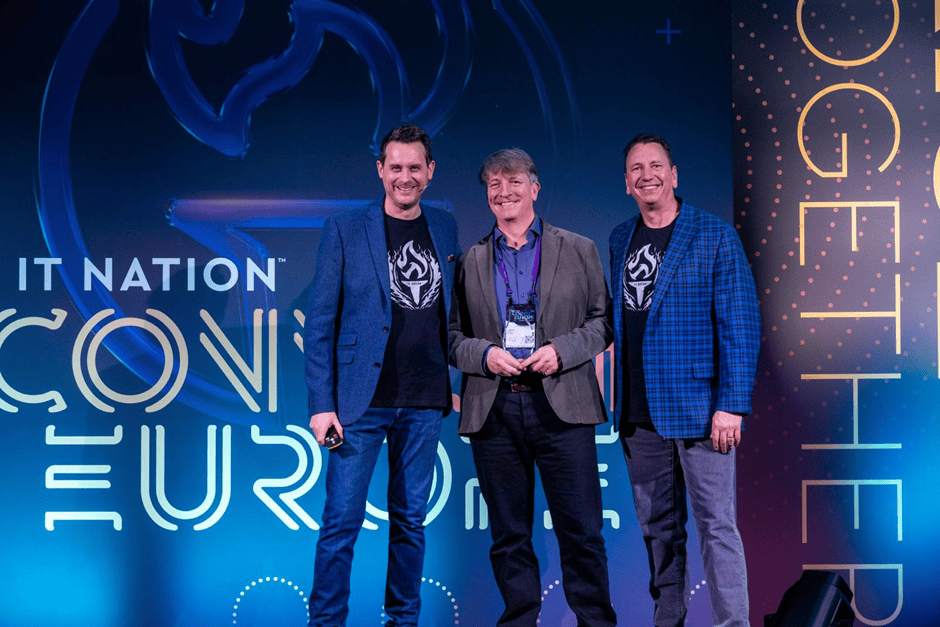
Looking for regular Stripe OLT security insights, straight to your inbox? Why not sign up for our newsletter, Access Granted.