What happened and why it matters
For many UK SMEs, Cyber Essentials has become the baseline for demonstrating cyber security credibility. Whether required for public sector contracts, supply chain assurance, or simply to evidence good governance, the certification has long represented a clear, accessible route to showing you take security seriously.
Once again, Cyber Essentials is changing.
From April 27th 2026, IASME is introducing an updated question set conducted in collaboration with the NCSC for Cyber Essentials – known as the Danzell question set – alongside revisions to the Requirements for IT Infrastructure.
The recent changes aim to raise the standard in key areas, including secure configuration, vulnerability management, identity controls and scope transparency – to improve the overall integrity of the certification process.
For UK SME CISOs and CTOs, the message is simple – Cyber Essentials is tightening, and operational maturity now matters more than ever.
Let’s explore these changes below:
1. Secure Configuration – Removal of Unnecessary Software
Secure configuration has always been a core Cyber Essentials control. What changes in 2026 is the explicit requirement to remove or disable unnecessary software across in-scope devices.
This includes vendor-installed utilities and bundled applications that:
- Run with elevated privileges
- Introduce attack surface
- Are not required for business use
Default installs are no longer acceptable simply because they are “standard”. Organisations must be able to demonstrate that devices are deliberately hardened.
2. Vulnerability Management – The 14 Day Rule
The most impactful operational change is around patching.
Under the 2026 update, all software on in-scope devices must be updated within 14 days where:
- The vendor describes the vulnerability as critical or high risk
- The vulnerability has a CVSS v3 base score of 7 or above
- The vendor provides no severity details
This is a clear, measurable compliance requirement.
It moves Cyber Essentials from “apply updates in a timely manner” to a defined remediation window aligned with NCSC guidance on high-risk vulnerabilities.
For many SMEs, this introduces the need for continuous vulnerability visibility – not just patching operating systems, but routers and firewall firmware, applications, and third-party software as well.
3. Continuous Vulnerability Scanning – Not Just Audit-Time Fixes
Historically, Cyber Essentials Plus audits have used vulnerability scanning tools to identify weaknesses during assessment.
The updated expectation is that equivalent vulnerability scanning and remediation should already be in place – continuously – not introduced temporarily for audit purposes. This effectively embeds scanning and weekly remediation cycles into day-to-day operations.
This effectively embeds scanning and weekly remediation cycles into day-to-day operations.
4. Identity Controls and MFA – No More Grey Areas
The updated question set removes ambiguity around multi-factor authentication.
Where MFA is available, it must be enabled. Failure to enforce it where technically possible will result in failure.
This aligns with broader NCSC guidance on identity-first security and phishing-resistant authentication.
5. Scope Transparency and Ongoing Compliance
The 2026 changes also strengthen scope clarity:
- More detailed scope descriptions which will be visible on the digital certification platform
- Clear identification of included legal entities with individual certificates available for each legal entity within a larger scope
- Explicit recognition of cloud services within scope
- Assessors will test a new random sample to ensure the updates identified have been applied wider than to just the devices in the original sample
In addition, directors or senior leaders must confirm that controls will be maintained throughout the certification period – not just at point of assessment.
This reinforces Cyber Essentials as an ongoing security posture commitment rather than a point-in-time certificate.
What This Means Operationally for UK SMEs
For many SMEs, the impact will be felt in three areas:
- Asset visibility – knowing exactly what software is installed across the estate
- Patch discipline – proving 14-day remediation for high-risk vulnerabilities
- Configuration control – demonstrating hardened, minimal device builds
Without automation and consistent monitoring, these requirements become difficult to evidence.
Embedding the 2026 Controls in Practice
The 2026 update reinforces areas we have long considered foundational to SME cyber resilience: secure configuration discipline and consistent vulnerability remediation.
1. Secure Configurations
The revised requirements place greater emphasis on demonstrable control over secure configuration.
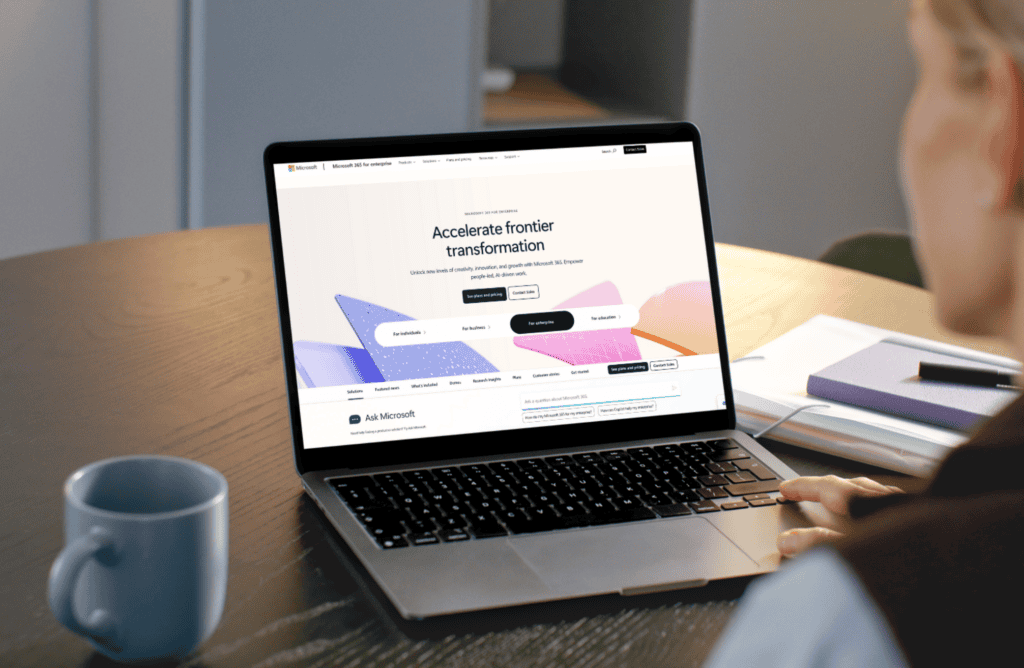
- Utilise a toolset like Inforcer – an M365 Security Management solution that backs up configuration profiles and Conditional Access policies, providing clear reporting aligned to the Cyber Essentials baseline and reducing configuration drift.
- Use Clean Device Builds – known as “vanilla” Windows installs – removing vendor-installed software at source. This reduces unnecessary attack surface and makes ongoing vulnerability remediation more consistent.
- Implement Sanctioned Software Management – using controlled allow-lists so that only approved applications can run. This reduces shadow IT, limits unauthorised software execution, and strengthens scope transparency under Cyber Essentials.
2. Vulnerability Management
One of the most common gaps within SME environments is inconsistency. Patching often happens monthly, reactively, or only when an issue becomes visible. Third-party applications drift out of date. Devices fall behind policy. Over time, this creates silent exposure – particularly as attackers increasingly target known, unpatched vulnerabilities.
The 2026 update makes clear that vulnerability management must be systematic, timely and demonstrable.
To address you should:
- Do Weekly Vulnerability Remediations – leveraging Microsoft licensing to review and remediate vulnerabilities across the estate on weekly cycles
Cyber Essentials 2026 is a necessary tightening of baseline security standards, and the direction is clear…
- Make fewer assumptions
- Ensure less ambiguity
- Define remediation timelines
- Ensure ongoing compliance
For UK SMEs, early preparation will reduce audit friction and strengthen genuine cyber resilience.
The organisations that treat this as an operational maturity exercise – not just a certification renewal – will be best positioned in 2026 and beyond.
If you’re looking for Cyber Essentials support to get you through this latest round of changes, get in touch today.